怎么樣分配公網(wǎng)證書(shū)基于負(fù)載均衡-Keepalived-Haproxy-創(chuàng)新互聯(lián)
下文給大家?guī)?lái)怎么樣分配公網(wǎng)證書(shū)基于負(fù)載均衡-Keepalived-Haproxy,希望能夠給大家在實(shí)際運(yùn)用中帶來(lái)一定的幫助,負(fù)載均衡涉及的東西比較多,理論也不多,網(wǎng)上有很多書(shū)籍,今天我們就用創(chuàng)新互聯(lián)在行業(yè)內(nèi)累計(jì)的經(jīng)驗(yàn)來(lái)做一個(gè)解答。

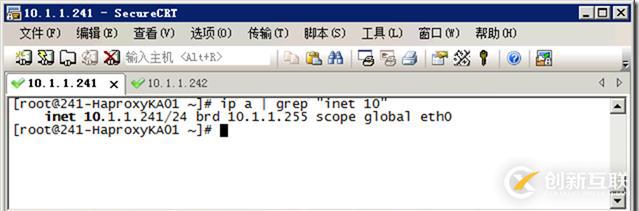
241-HaproxyKA01
242-HaproxyKA02
同樣配置。
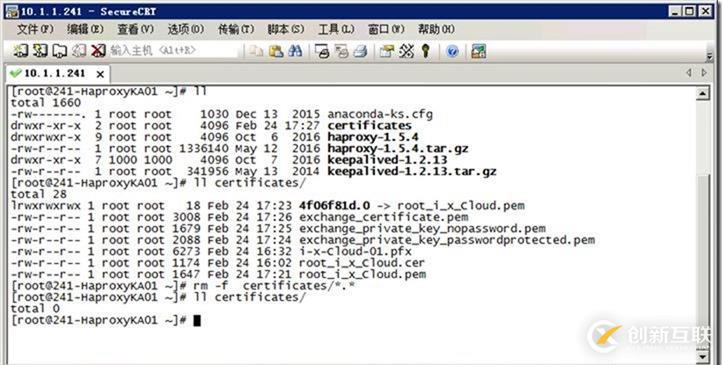
// 0. 刪除文件
//刪除舊證書(shū):
ll certificates/
rm -f certificates/*.* //刪除所有
ll certificates/
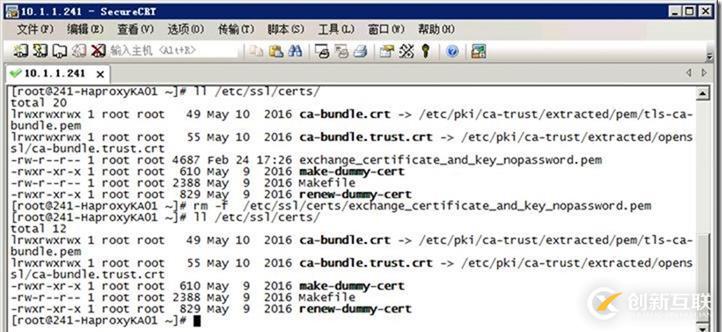
//刪除證書(shū)
ll /etc/ssl/certs/
rm -f /etc/ssl/certs/exchange_certificate_and_key_nopassword.pem //刪除此文件
ll /etc/ssl/certs/
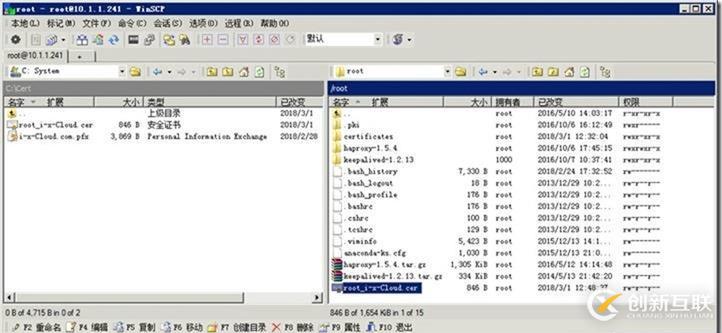
// 1.下載 CA 證書(shū)(根證書(shū))

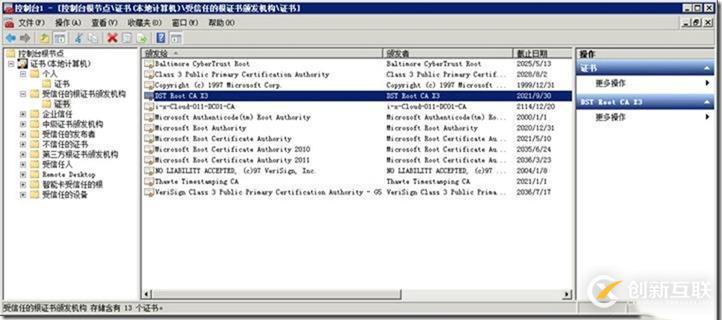
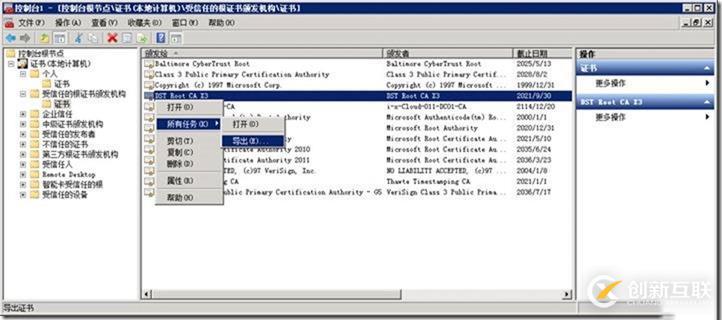
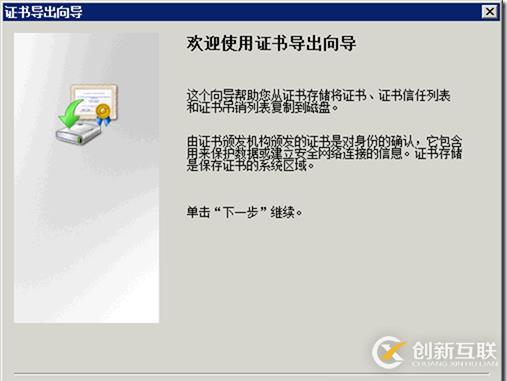
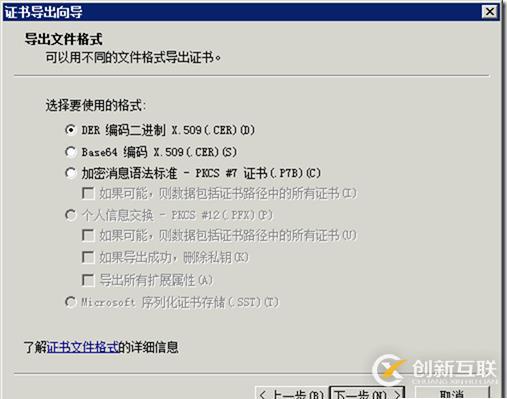
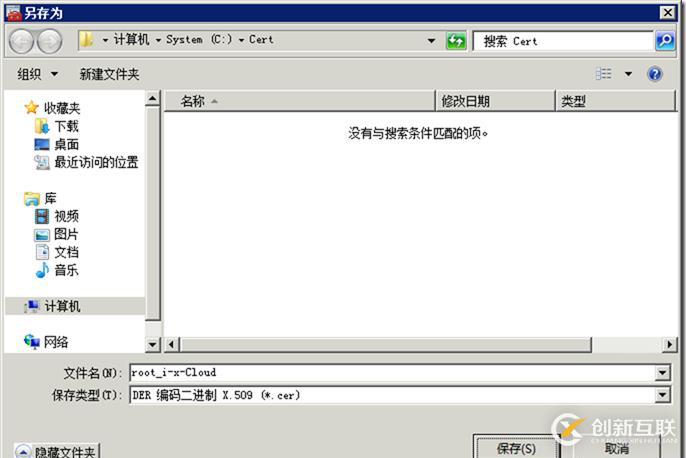
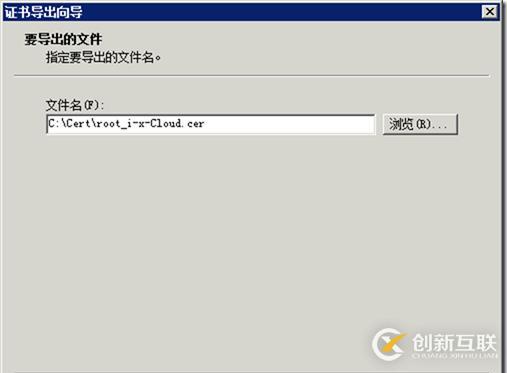
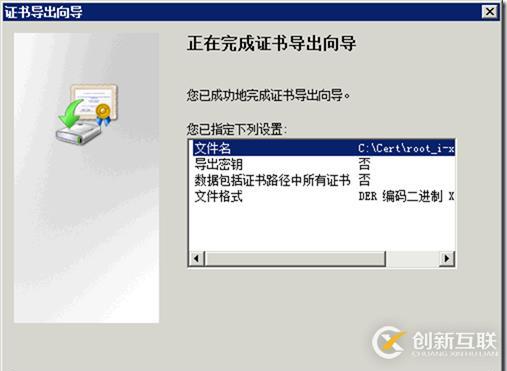
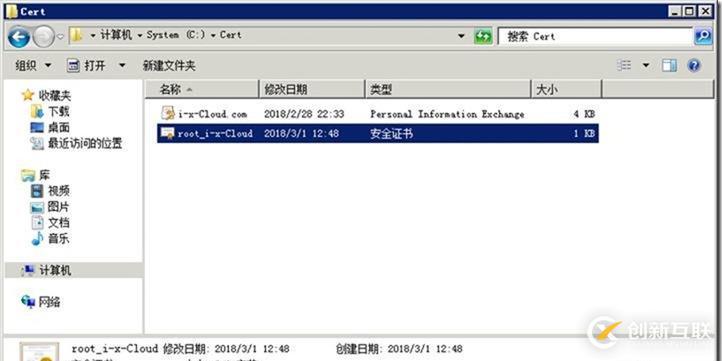
root_i-x-Cloud.cer
上傳到 /root/
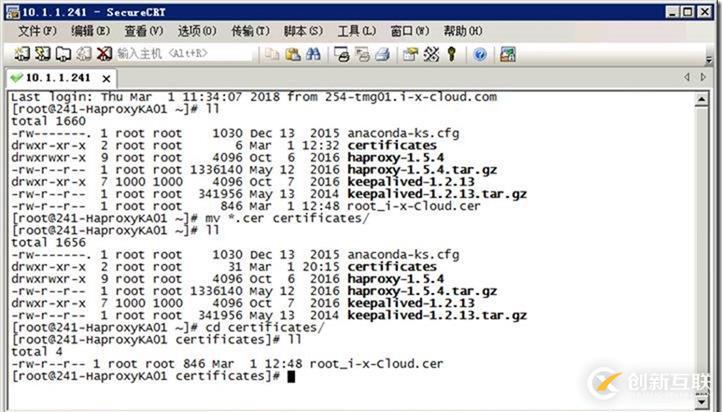
ls *.cer -l
mv *.cer certificates/
cd certificates
ll
[root@241-HaproxyKA01 ~]# ll
total 1660
-rw-------. 1 root root 1030 Dec 13 2015 anaconda-ks.cfg
drwxr-xr-x 2 root root 6 Feb 24 17:18 certificates
drwxrwxr-x 9 root root 4096 Oct 6 2016 haproxy-1.5.4
-rw-r--r-- 1 root root 1336140 May 12 2016 haproxy-1.5.4.tar.gz
drwxr-xr-x 7 1000 1000 4096 Oct 7 2016 keepalived-1.2.13
-rw-r--r-- 1 root root 341956 May 13 2014 keepalived-1.2.13.tar.gz
-rw-r--r-- 1 root root 1174 Feb 24 16:02 root_i_x_Cloud.cer
[root@241-HaproxyKA01 ~]# mv *.cer certificates/
[root@241-HaproxyKA01 ~]# cd certificates/
[root@241-HaproxyKA01 certificates]# ll
total 4
-rw-r--r-- 1 root root 1174 Feb 24 16:02 root_i_x_Cloud.cer
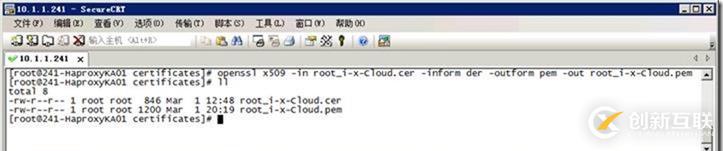
// 2. 將cer轉(zhuǎn)為pem (根證書(shū))
openssl x509 -in root_i-x-Cloud.cer -inform der -outform pem -out root_i-x-Cloud.pem
ll
[root@241-HaproxyKA01 certificates]# openssl x509 -in root_i-x-Cloud.cer -inform der -outform pem -out root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]# ll
total 8
-rw-r--r-- 1 root root 1174 Feb 24 16:02 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1647 Feb 24 17:21 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
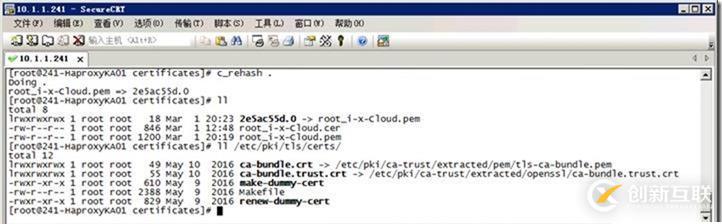
// 3. 重新生成hash
[root@241-HaproxyKA01 certificates]# c_rehash .
Doing .
root_i-x-Cloud.pem => 2e5ac55d.0
[root@241-HaproxyKA01 certificates]# ll
total 8
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]# ll /etc/pki/tls/certs/
total 12
lrwxrwxrwx 1 root root 49 May 10 2016 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
lrwxrwxrwx 1 root root 55 May 10 2016 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
-rwxr-xr-x 1 root root 610 May 9 2016 make-dummy-cert
-rw-r--r-- 1 root root 2388 May 9 2016 Makefile
-rwxr-xr-x 1 root root 829 May 9 2016 renew-dummy-cert
[root@241-HaproxyKA01 certificates]#
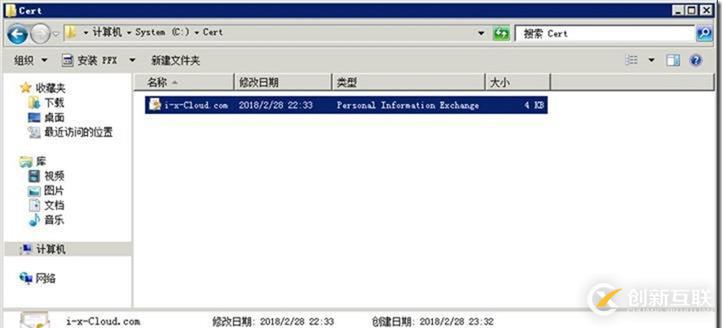
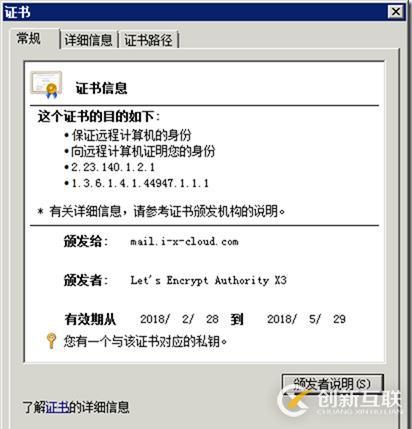
// 4. 導(dǎo)出證書(shū)(設(shè)置密碼:Aa123456)//密碼不能為1.
i-x-Cloud.com.pfx
上傳證書(shū):/root/certificates/

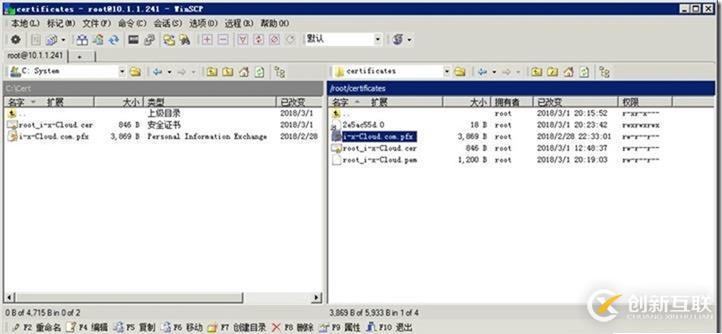
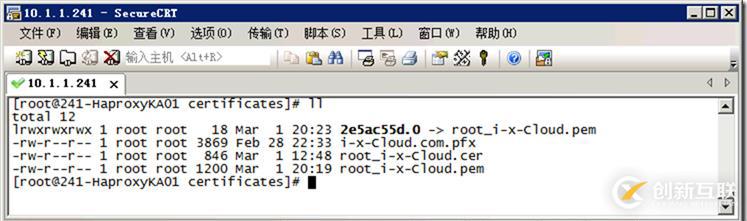
[root@241-HaproxyKA01 certificates]# ll
total 12
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3869 Feb 28 22:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
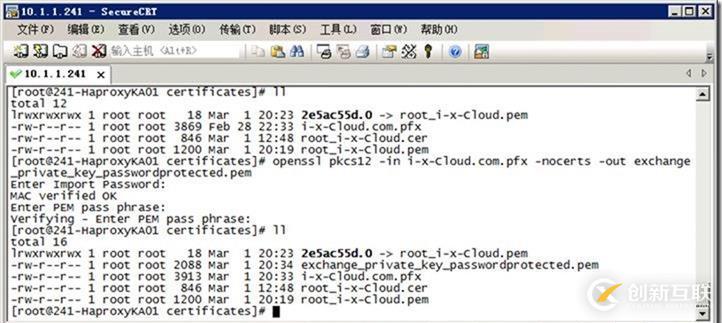
// 5. 將pfx轉(zhuǎn)為pem
openssl pkcs12 -in i-x-Cloud.com.pfx -nocerts -out exchange_private_key_passwordprotected.pem
Aa123456
[root@241-HaproxyKA01 certificates]# ll
total 12
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3869 Feb 28 22:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]# openssl pkcs12 -in i-x-Cloud.com.pfx -nocerts -out exchange_private_key_passwordprotected.pem
Enter Import Password:
MAC verified OK
Enter PEM pass phrase:
Verifying - Enter PEM pass phrase:
[root@241-HaproxyKA01 certificates]# ll
total 16
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
// 6. 移出密碼保護(hù)
openssl rsa -in exchange_private_key_passwordprotected.pem -out exchange_private_key_nopassword.pem
[root@241-HaproxyKA01 certificates]# openssl rsa -in exchange_private_key_passwordprotected.pem -out exchange_private_key_nopassword.pem
Enter pass phrase for exchange_private_key_passwordprotected.pem:
writing RSA key
[root@241-HaproxyKA01 certificates]# ll
total 20
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
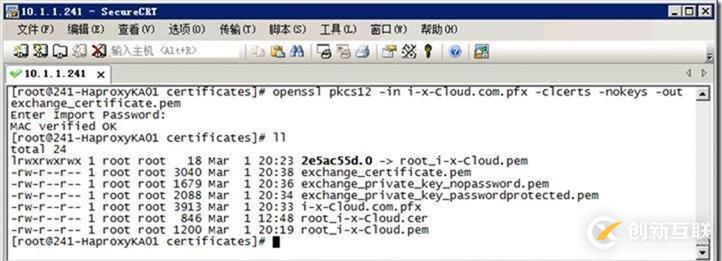
// 7. 解壓這個(gè)pfx文件,我們需要提供憑證。
openssl pkcs12 -in i-x-Cloud.com.pfx -clcerts -nokeys -out exchange_certificate.pem
ll
[root@241-HaproxyKA01 certificates]# openssl pkcs12 -in i-x-Cloud.com.pfx -clcerts -nokeys -out exchange_certificate.pem
Enter Import Password:
MAC verified OK
[root@241-HaproxyKA01 certificates]# ll
total 24
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3040 Mar 1 20:38 exchange_certificate.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
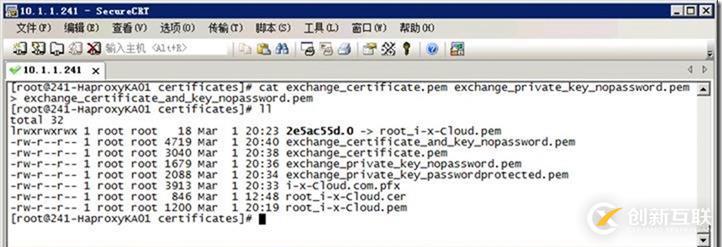
// 8. 通過(guò)將exchange_certificate.pem和exchange_private_key_nopassword.pem產(chǎn)生exchange_certificate_and_key_nopassword.pem。
cat exchange_certificate.pem exchange_private_key_nopassword.pem > exchange_certificate_and_key_nopassword.pem
ll
[root@241-HaproxyKA01 certificates]# cat exchange_certificate.pem exchange_private_key_nopassword.pem > exchange_certificate_and_key_nopassword.pem
[root@241-HaproxyKA01 certificates]# ll
total 32
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 4719 Mar 1 20:40 exchange_certificate_and_key_nopassword.pem
-rw-r--r-- 1 root root 3040 Mar 1 20:38 exchange_certificate.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
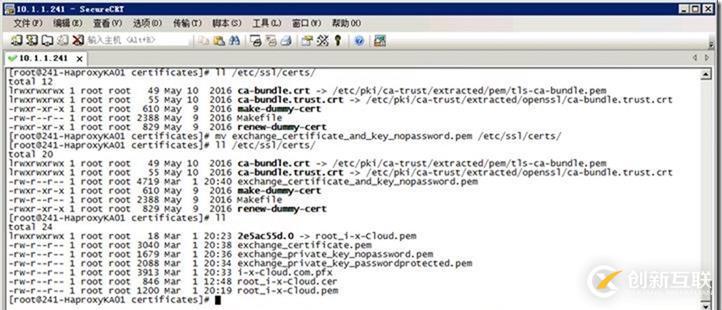
// 9. 復(fù)制到文件夾中
ll /etc/ssl/certs/
rm -f /etc/ssl/certs/exchange_certificate_and_key_nopassword.pem
mv exchange_certificate_and_key_nopassword.pem /etc/ssl/certs/
ll /etc/ssl/certs/
ll
[root@241-HaproxyKA01 certificates]# ll /etc/ssl/certs/
total 12
lrwxrwxrwx 1 root root 49 May 10 2016 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
lrwxrwxrwx 1 root root 55 May 10 2016 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
-rwxr-xr-x 1 root root 610 May 9 2016 make-dummy-cert
-rw-r--r-- 1 root root 2388 May 9 2016 Makefile
-rwxr-xr-x 1 root root 829 May 9 2016 renew-dummy-cert
[root@241-HaproxyKA01 certificates]# mv exchange_certificate_and_key_nopassword.pem /etc/ssl/certs/
[root@241-HaproxyKA01 certificates]# ll /etc/ssl/certs/
total 20
lrwxrwxrwx 1 root root 49 May 10 2016 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
lrwxrwxrwx 1 root root 55 May 10 2016 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
-rw-r--r-- 1 root root 4719 Mar 1 20:40 exchange_certificate_and_key_nopassword.pem
-rwxr-xr-x 1 root root 610 May 9 2016 make-dummy-cert
-rw-r--r-- 1 root root 2388 May 9 2016 Makefile
-rwxr-xr-x 1 root root 829 May 9 2016 renew-dummy-cert
[root@241-HaproxyKA01 certificates]# ll
total 24
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3040 Mar 1 20:38 exchange_certificate.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
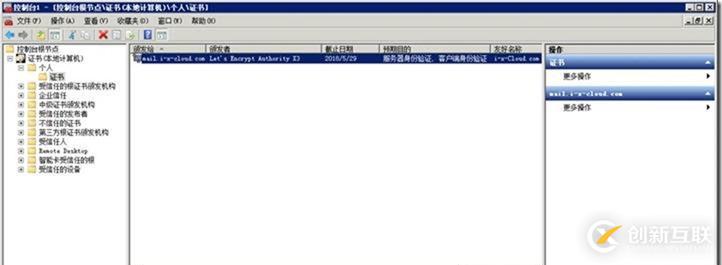
// 10. 測(cè)試
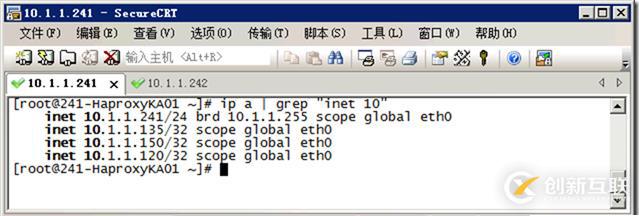
[root@241-HaproxyKA01 ~]# ip a | grep "inet 10"
inet 10.1.1.241/24 brd 10.1.1.255 scope global eth0
inet 10.1.1.135/32 scope global eth0
inet 10.1.1.150/32 scope global eth0
inet 10.1.1.120/32 scope global eth0
[root@241-HaproxyKA01 ~]#
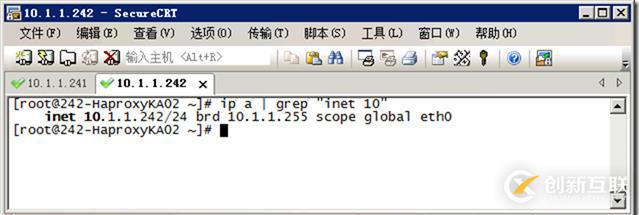
[root@242-HaproxyKA02 ~]# ip a | grep "inet 10"
inet 10.1.1.242/24 brd 10.1.1.255 scope global eth0
[root@242-HaproxyKA02 ~]#
[root@241-HaproxyKA01 ~]# ip a | grep "inet 10"
inet 10.1.1.241/24 brd 10.1.1.255 scope global eth0
[root@241-HaproxyKA01 ~]#
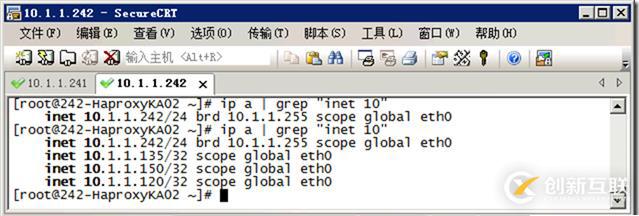
[root@242-HaproxyKA02 ~]# ip a | grep "inet 10"
inet 10.1.1.242/24 brd 10.1.1.255 scope global eth0
[root@242-HaproxyKA02 ~]# ip a | grep "inet 10"
inet 10.1.1.242/24 brd 10.1.1.255 scope global eth0
inet 10.1.1.135/32 scope global eth0
inet 10.1.1.150/32 scope global eth0
inet 10.1.1.120/32 scope global eth0
[root@242-HaproxyKA02 ~]#
看了以上關(guān)于怎么樣分配公網(wǎng)證書(shū)基于負(fù)載均衡-Keepalived-Haproxy,如果大家還有什么地方需要了解的可以在創(chuàng)新互聯(lián)行業(yè)資訊里查找自己感興趣的或者找我們的專業(yè)技術(shù)工程師解答的,創(chuàng)新互聯(lián)技術(shù)工程師在行業(yè)內(nèi)擁有十幾年的經(jīng)驗(yàn)了。創(chuàng)新互聯(lián)官網(wǎng)鏈接www.yisu.com
另外有需要云服務(wù)器可以了解下創(chuàng)新互聯(lián)cdcxhl.cn,海內(nèi)外云服務(wù)器15元起步,三天無(wú)理由+7*72小時(shí)售后在線,公司持有idc許可證,提供“云服務(wù)器、裸金屬服務(wù)器、高防服務(wù)器、香港服務(wù)器、美國(guó)服務(wù)器、虛擬主機(jī)、免備案服務(wù)器”等云主機(jī)租用服務(wù)以及企業(yè)上云的綜合解決方案,具有“安全穩(wěn)定、簡(jiǎn)單易用、服務(wù)可用性高、性價(jià)比高”等特點(diǎn)與優(yōu)勢(shì),專為企業(yè)上云打造定制,能夠滿足用戶豐富、多元化的應(yīng)用場(chǎng)景需求。
當(dāng)前名稱:怎么樣分配公網(wǎng)證書(shū)基于負(fù)載均衡-Keepalived-Haproxy-創(chuàng)新互聯(lián)
轉(zhuǎn)載來(lái)源:http://chinadenli.net/article0/eoeoo.html
成都網(wǎng)站建設(shè)公司_創(chuàng)新互聯(lián),為您提供網(wǎng)站設(shè)計(jì)公司、ChatGPT、全網(wǎng)營(yíng)銷(xiāo)推廣、虛擬主機(jī)、網(wǎng)站導(dǎo)航、網(wǎng)頁(yè)設(shè)計(jì)公司
聲明:本網(wǎng)站發(fā)布的內(nèi)容(圖片、視頻和文字)以用戶投稿、用戶轉(zhuǎn)載內(nèi)容為主,如果涉及侵權(quán)請(qǐng)盡快告知,我們將會(huì)在第一時(shí)間刪除。文章觀點(diǎn)不代表本網(wǎng)站立場(chǎng),如需處理請(qǐng)聯(lián)系客服。電話:028-86922220;郵箱:631063699@qq.com。內(nèi)容未經(jīng)允許不得轉(zhuǎn)載,或轉(zhuǎn)載時(shí)需注明來(lái)源: 創(chuàng)新互聯(lián)
猜你還喜歡下面的內(nèi)容
- web中Math函數(shù)的作用是什么-創(chuàng)新互聯(lián)
- Python中excel和shp如何使用在matplotlib-創(chuàng)新互聯(lián)
- web開(kāi)發(fā)中如何解決瀏覽器會(huì)自動(dòng)填充密碼的問(wèn)題-創(chuàng)新互聯(lián)
- 把excel表格里的數(shù)據(jù)導(dǎo)入sql數(shù)據(jù)庫(kù)的兩種方法分別是什么-創(chuàng)新互聯(lián)
- Lync學(xué)習(xí)資料分享-創(chuàng)新互聯(lián)
- 目前l(fā)inux發(fā)行版默認(rèn)使用的文件系統(tǒng)是哪一個(gè)-創(chuàng)新互聯(lián)
- jsp中獲得的路徑的方法-創(chuàng)新互聯(lián)

- 企業(yè)處理網(wǎng)站策劃存在的三個(gè)誤區(qū) 2016-02-20
- 網(wǎng)站建設(shè)前期的網(wǎng)站策劃要怎么進(jìn)行? 2022-08-31
- 淄博網(wǎng)站建設(shè)-網(wǎng)站策劃說(shuō)明書(shū)的書(shū)寫(xiě) 2021-11-16
- 網(wǎng)站策劃的九個(gè)步驟 2016-09-09
- 新網(wǎng)站策劃市場(chǎng)研究網(wǎng)站用戶體驗(yàn)設(shè)計(jì) 2014-05-20
- 企業(yè)建設(shè)網(wǎng)站策劃需要的5個(gè)步驟 2015-07-27
- 企業(yè)網(wǎng)站建設(shè)怎樣做網(wǎng)站策劃方案 2022-05-29
- 企業(yè)網(wǎng)站策劃必須掌握好“三個(gè)核心”原則 2022-01-16
- 移動(dòng)互聯(lián)網(wǎng)時(shí)代建設(shè)移動(dòng)網(wǎng)站策劃該怎么做 2021-11-06
- 移動(dòng)互聯(lián)網(wǎng)時(shí)代建設(shè)移動(dòng)網(wǎng)站策劃該怎么做? 2022-11-29
- 網(wǎng)站策劃的主要是什么 2021-06-13
- SEO決定網(wǎng)站策劃與優(yōu)化要素有哪些 2021-11-19